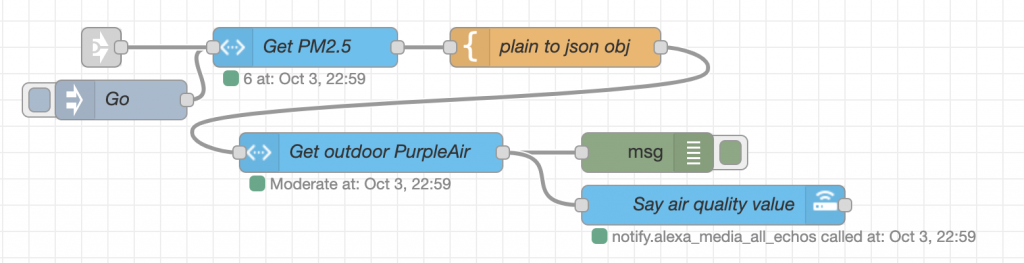
Simple example of how to make Alexa talk (TTS, Text To Speech) in Node Red with the ‘node-red-contrib-alexa-remote2’ palette.
You’ll have to change the account and cookie file to work with your setup. But this shows which nodes and fields to populate.
To send to all Echo devices, I use the device “Everywhere” (see the debug output of “Get Echo Devices”).
If you don’t hear anything, try “Refresh alexa remote2 cookie”. I have a flow that auto-refreshes the cookie every 2 hours.
How-to import node red code: https://www.youtube.com/watch?v=_uN–N7YE24
Import this code:
[
{
"id": "d327c2c8.b617a",
"type": "tab",
"label": "Alexa TTS example",
"disabled": false,
"info": ""
},
{
"id": "185e5c5.ca37da4",
"type": "alexa-remote-init",
"z": "d327c2c8.b617a",
"name": "Refresh alexa remote2 cookie",
"account": "204c43f9.0e87dc",
"option": "refresh",
"x": 350,
"y": 120,
"wires": [
[
"ca0268c3.6a75b8"
]
]
},
{
"id": "aa1de4f1.d53768",
"type": "inject",
"z": "d327c2c8.b617a",
"name": "Go",
"topic": "",
"payload": "",
"payloadType": "date",
"repeat": "",
"crontab": "",
"once": false,
"onceDelay": 0.1,
"x": 130,
"y": 120,
"wires": [
[
"185e5c5.ca37da4"
]
]
},
{
"id": "ca0268c3.6a75b8",
"type": "debug",
"z": "d327c2c8.b617a",
"name": "",
"active": true,
"tosidebar": true,
"console": false,
"tostatus": false,
"complete": "true",
"targetType": "full",
"x": 550,
"y": 120,
"wires": []
},
{
"id": "573b246e.f1f59c",
"type": "inject",
"z": "d327c2c8.b617a",
"name": "Go",
"topic": "",
"payload": "",
"payloadType": "date",
"repeat": "",
"crontab": "",
"once": false,
"onceDelay": 0.1,
"x": 130,
"y": 180,
"wires": [
[
"772e0bd4.b6e5d4"
]
]
},
{
"id": "772e0bd4.b6e5d4",
"type": "alexa-remote-routine",
"z": "d327c2c8.b617a",
"name": "\"Hello\", office Dot",
"account": "204c43f9.0e87dc",
"routineNode": {
"type": "speak",
"payload": {
"type": "regular",
"text": {
"type": "str",
"value": "Hello"
},
"devices": {
"type": "str",
"value": "DONN's Echo Dot"
}
}
},
"x": 330,
"y": 180,
"wires": [
[]
]
},
{
"id": "7b5e0b7b.f95e24",
"type": "inject",
"z": "d327c2c8.b617a",
"name": "Go",
"topic": "",
"payload": "",
"payloadType": "date",
"repeat": "",
"crontab": "",
"once": false,
"onceDelay": 0.1,
"x": 130,
"y": 60,
"wires": [
[
"f9cb8443.8252d8"
]
]
},
{
"id": "f9cb8443.8252d8",
"type": "alexa-remote-echo",
"z": "d327c2c8.b617a",
"name": "",
"account": "204c43f9.0e87dc",
"config": {
"option": "get",
"value": {
"what": "device",
"device": {
"type": "str",
"value": "ALEXA_ALL_DSN"
}
}
},
"x": 290,
"y": 60,
"wires": [
[
"e48dfccc.4bd7"
]
]
},
{
"id": "e48dfccc.4bd7",
"type": "debug",
"z": "d327c2c8.b617a",
"name": "",
"active": true,
"tosidebar": true,
"console": false,
"tostatus": false,
"complete": "true",
"targetType": "full",
"x": 450,
"y": 60,
"wires": []
},
{
"id": "204c43f9.0e87dc",
"type": "alexa-remote-account",
"z": "",
"name": "D acct",
"authMethod": "proxy",
"proxyOwnIp": "172.16.0.203",
"proxyPort": "3457",
"cookieFile": "/config/alexa_cookies2.txt",
"refreshInterval": "3",
"alexaServiceHost": "pitangui.amazon.com",
"amazonPage": "amazon.com",
"acceptLanguage": "en-US",
"userAgent": "",
"useWsMqtt": "on",
"autoInit": "on"
}
]
For SSML examples, see: https://github.com/586837r/node-red-contrib-alexa-remote2/blob/master/examples.md
Detailed video howto: https://www.youtube.com/watch?v=vj9K0O_3zxI
#